Next-Generation Security Solutions
Comprehensive protection powered by AI-driven threat detection and quantum-resistant encryption protocols
Quantum Security
Advanced quantum-resistant algorithms protect against future cryptographic attacks with post-quantum encryption standards.
- 256-bit quantum encryption
- Real-time threat analysis
- Zero-trust architecture
AI-Powered Detection
Machine learning algorithms continuously adapt to emerging threats, providing predictive security measures before attacks occur.
- Behavioral anomaly detection
- Predictive threat modeling
- Automated response systems
Blockchain Verification
Immutable patch verification through distributed ledger technology ensures authentic updates and prevents tampering.
- Cryptographic verification
- Tamper-proof audit trails
- Decentralized validation
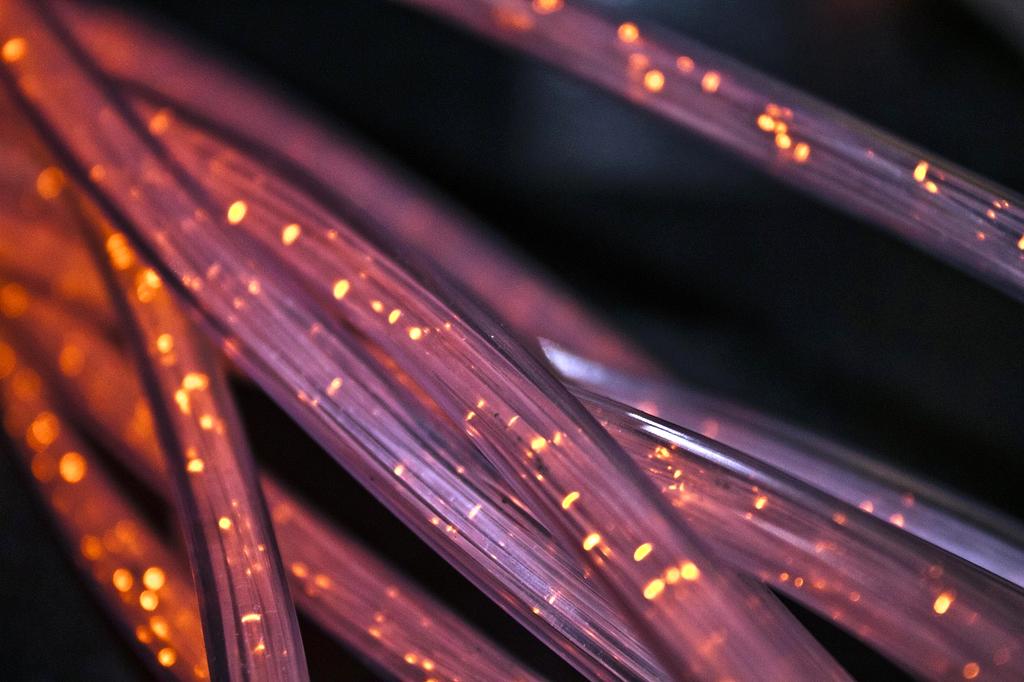
Edge Computing
Distributed processing at network edges reduces latency and improves security response times for critical infrastructure.
- Sub-millisecond response
- Distributed processing
- Edge-to-cloud synchronization
Biometric Authentication
Multi-modal biometric systems including facial recognition, fingerprint, and voice pattern analysis for ultimate access control.
- Multi-factor biometrics
- Liveness detection
- Privacy-preserving matching
Neural Firewall
Self-learning network protection that evolves with threat landscapes, automatically updating defense strategies in real-time.
- Adaptive threat blocking
- Pattern recognition
- Self-optimizing rules
99.97%
Threat Detection Rate
<0.3ms
Response Time
256-bit
Quantum Encryption
24/7
Continuous Monitoring
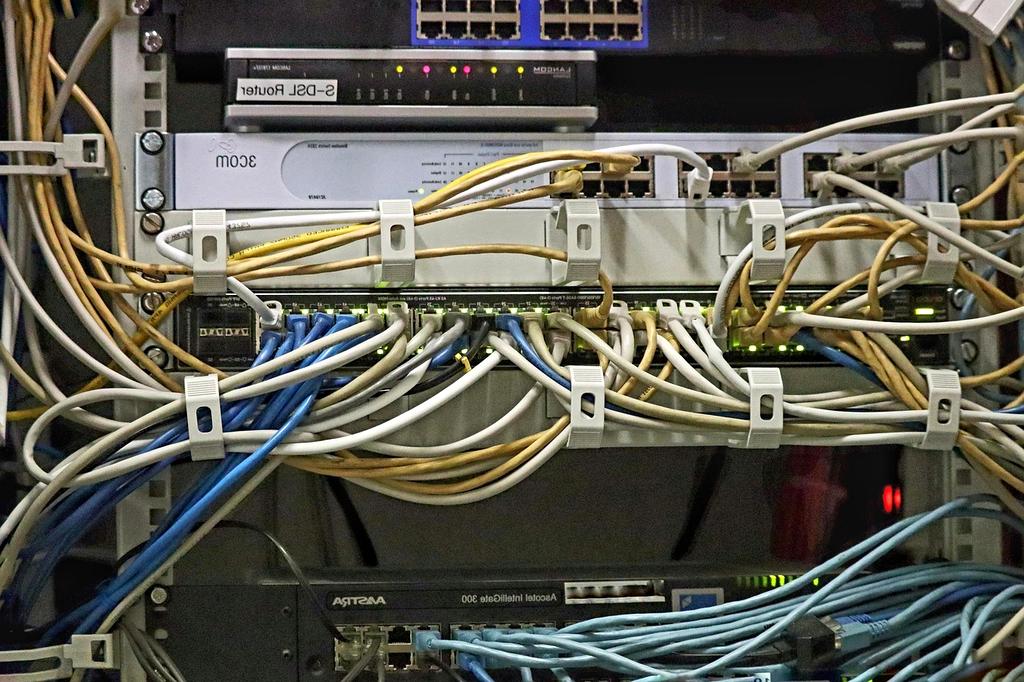
Intelligent Automation Pipeline
Our advanced orchestration platform seamlessly integrates with your existing infrastructure, delivering autonomous patch deployment with predictive failure prevention and self-healing capabilities.

Seamless Platform Integration
Cloud Platforms




Container Orchestration




Monitoring & Observability




Predictive Analysis
Machine learning algorithms analyze historical deployment patterns to predict optimal maintenance windows and potential compatibility issues before they occur.
- Behavioral pattern recognition
- Resource utilization forecasting
- Impact simulation modeling
Self-Healing Systems
Autonomous recovery mechanisms detect and resolve deployment failures instantly, maintaining service continuity through intelligent rollback and retry strategies.
- Automatic failure detection
- Intelligent rollback procedures
- Service mesh integration

Compliance Automation
Built-in regulatory compliance engines ensure all updates meet industry standards including SOX, HIPAA, PCI-DSS, and GDPR requirements with automated documentation.
- Regulatory framework mapping
- Automated audit trails
- Compliance score tracking
Secure Your Infrastructure Today
Get personalized patch management solutions tailored to your business needs. Our security experts will contact you within 24 hours to discuss your requirements.